Patient Data Breaches: GDPR Reporting Rules

Key Takeaways
Patient Data Breaches: GDPR Reporting Rules
Protecting patient data is non-negotiable. Under GDPR, healthcare SaaS platforms must follow strict rules to manage and report breaches involving sensitive patient information. Failing to act quickly can result in fines of up to €10 million or 2% of global annual revenue. Here’s what you need to know:
- 72-Hour Deadline: Data controllers must notify authorities within 72 hours of becoming aware of a breach. Processors must alert controllers immediately.
- What Counts as a Breach: Includes unauthorized access, sending records to the wrong person, ransomware attacks, or losing unencrypted devices.
- When to Notify Patients: If the breach poses a high risk to individuals, patients must be informed promptly with clear guidance on protecting themselves.
- Incident Response Plan: A clear, tested plan is critical. It should include detection systems, staff training, and detailed reporting procedures.
Failing to comply isn’t just about fines - it’s about protecting individuals from identity theft, fraud, and exposure of sensitive medical details. Read on for detailed steps to manage breaches effectively.
How to Handle a Data Breach - GDPR Procedures | Privacy & Data Protection | CT Academy
sbb-itb-8f61039
The 72-Hour Breach Notification Requirement
When a breach happens, every second counts. Under GDPR, data controllers must notify the appropriate supervisory authority within 72 hours of becoming aware of the breach. This deadline applies to all days, including weekends and public holidays. Failing to meet this timeframe can result in fines of up to €10 million or 2% of your organization's total global annual revenue - whichever is higher.
For healthcare SaaS platforms acting as data processors, the obligation is slightly different. Your role is to notify the data controller - usually the healthcare provider - immediately after identifying the breach. Once the controller is informed, their 72-hour window begins. This makes the moment of detection critically important.
When the 72-Hour Countdown Begins
The clock starts as soon as your organization becomes "aware" of the breach, not when your investigation is complete. According to the European Data Protection Board, "awareness" occurs when there is clear evidence that a security incident has compromised personal data. This means you can’t afford to wait for a full forensic analysis before notifying authorities. Regulators expect an initial report with the facts you have at the time, followed by updates as more details emerge.
To ensure compliance, document key details like the breach detection date, time, method of discovery, and the reasoning behind your determination of awareness. If the 72-hour deadline is missed, your notification must include an explanation for the delay. To avoid this, establish clear escalation procedures to alert your Data Protection Officer as soon as a potential incident is identified.
Required Information for Breach Reports
Once the 72-hour window begins, your report must include all currently available details. Here's what needs to be covered:
| Required Information Category | What You Must Include |
|---|---|
| Nature of the Breach | Specify the type of breach, categories of affected data (e.g., medical records), approximate number of individuals impacted, and the number of records compromised. |
| Contact Point | Provide the name, direct phone number, and email of your Data Protection Officer or another designated contact for follow-ups. |
| Likely Consequences | Outline potential risks to individuals, such as identity theft, fraud, unauthorized access to sensitive health information, or loss of control over personal data. |
| Measures Taken | Detail actions taken to contain the breach, along with proposed steps to prevent further harm and mitigate risks. |
When You Must Notify Patients About a Breach
In cases of high-risk breaches, notifying patients directly isn't just a recommendation - it's a requirement. If a breach is likely to cause serious harm to patients' rights or freedoms, those affected must be informed right away.
To assess whether a breach is high-risk, you need to consider two key factors: how severe the impact might be and how likely it is to occur. Breaches involving sensitive data, like health records or information protected by professional confidentiality, are especially concerning. The Information Commissioner's Office (ICO) puts it this way:
If the impact of the breach is more severe, the risk is higher; if the likelihood of the consequences is greater, then again the risk is higher.
Let’s look at when patient notification is necessary and when it’s not.
High-Risk Breaches That Require Patient Notification
High-risk breaches can lead to physical, financial, or emotional harm. According to UK GDPR Recital 85, these risks might include:
identity theft or fraud, financial loss, unauthorised reversal of pseudonymisation, damage to reputation, loss of confidentiality of personal data protected by professional secrecy or any other significant economic or social disadvantage to the natural person concerned.
For example, if sensitive medical data is accidentally made public, notifying the affected patients is essential.
When reaching out to patients, your message should be straightforward and easy to understand. Include the following details in your notification:
- A description of the breach
- Contact information for follow-up questions
- A summary of potential risks
- Steps patients can take to protect themselves, such as resetting passwords or watching for phishing attempts
When Patient Notification Is Not Required
Not all breaches require notifying patients, even if the supervisory authority has been informed. Here are some scenarios where patient notification might not be necessary:
- Data is secured: If strong encryption or other advanced security measures make the breached data unreadable, there’s no need to notify patients.
- Risk is mitigated: If immediate actions are taken to address the issue and reduce the risk, individual notifications can be skipped. For instance, the ICO describes a case where a medical professional accidentally sent the wrong records to a colleague. The error was reported right away, and the files were securely deleted, minimizing the risk so patient notification wasn’t required.
- Disproportionate effort: If contacting every affected patient would be overly burdensome, alternatives like a public notice or other effective methods may suffice.
Building a GDPR-Compliant Incident Response Plan
Creating a GDPR-compliant incident response plan is essential to avoid penalties that can reach up to €10 million or 2% of global revenue. It also ensures compliance with the 72-hour breach notification rule. This plan should address every step, from detecting a breach to documenting the response.
Core Elements of an Incident Response Plan
An effective incident response plan must include clear procedures for identifying breaches. This involves deploying systems to detect warning signs like unusual system activity, unauthorized file changes, or malware. Training staff is equally important - they need to recognize that breaches can include accidental data loss, unauthorized disclosure, or alterations to patient information.
Assigning roles is critical. Key roles like Incident Manager, Security Lead, Communications Lead, and Documentation Specialist ensure a swift and coordinated response when the 72-hour clock starts. These assignments clarify responsibilities, reducing delays during a crisis.
Your plan should also detail how to investigate and assess risks following a breach. This means quickly determining the type of data affected, the number of individuals impacted, and the potential risks involved. The findings will guide whether you need to notify the supervisory authority, the affected individuals, or both.
Internal reporting protocols are another cornerstone. Every employee should know how to report a suspected breach immediately to the Data Protection Officer (DPO) or the designated response team.
Containment and mitigation steps should be outlined in detail. Immediate actions might include remotely wiping lost devices, applying security patches, or isolating compromised systems. GDPR Article 33 requires that all breaches be documented - this includes the facts, outcomes, and remedial measures - regardless of whether the breach warrants external notification.
Lastly, your plan should evolve. Regular updates and testing are necessary to address new threats and changes in data handling practices.
Regular Testing and Plan Updates
A plan is only as good as its execution. To ensure it works when needed, make regular testing and updates part of your routine. Incorporate the plan into annual audits to address new security risks and any changes in how patient data is managed. Simulations are particularly useful for testing your team's ability to meet the 72-hour notification deadline.
After any breach, take time to evaluate what went wrong. The Information Commissioner's Office (ICO) emphasizes the importance of learning from incidents:
"Following a breach, you should always reflect and consider any lessons learned. In particular, whether your risk assessment process is comprehensive enough, as well as how effective your mitigations and controls are."
Maintain a detailed breach log, recording all incidents - even minor ones that don't require regulatory notification. This log can help identify patterns, refine controls, and demonstrate compliance during audits.
Finally, adopt continuous monitoring tools to detect vulnerabilities before they escalate into breaches. Regularly test your detection systems to ensure they can spot potential issues as they arise.
GDPR vs. HIPAA: Breach Reporting Differences
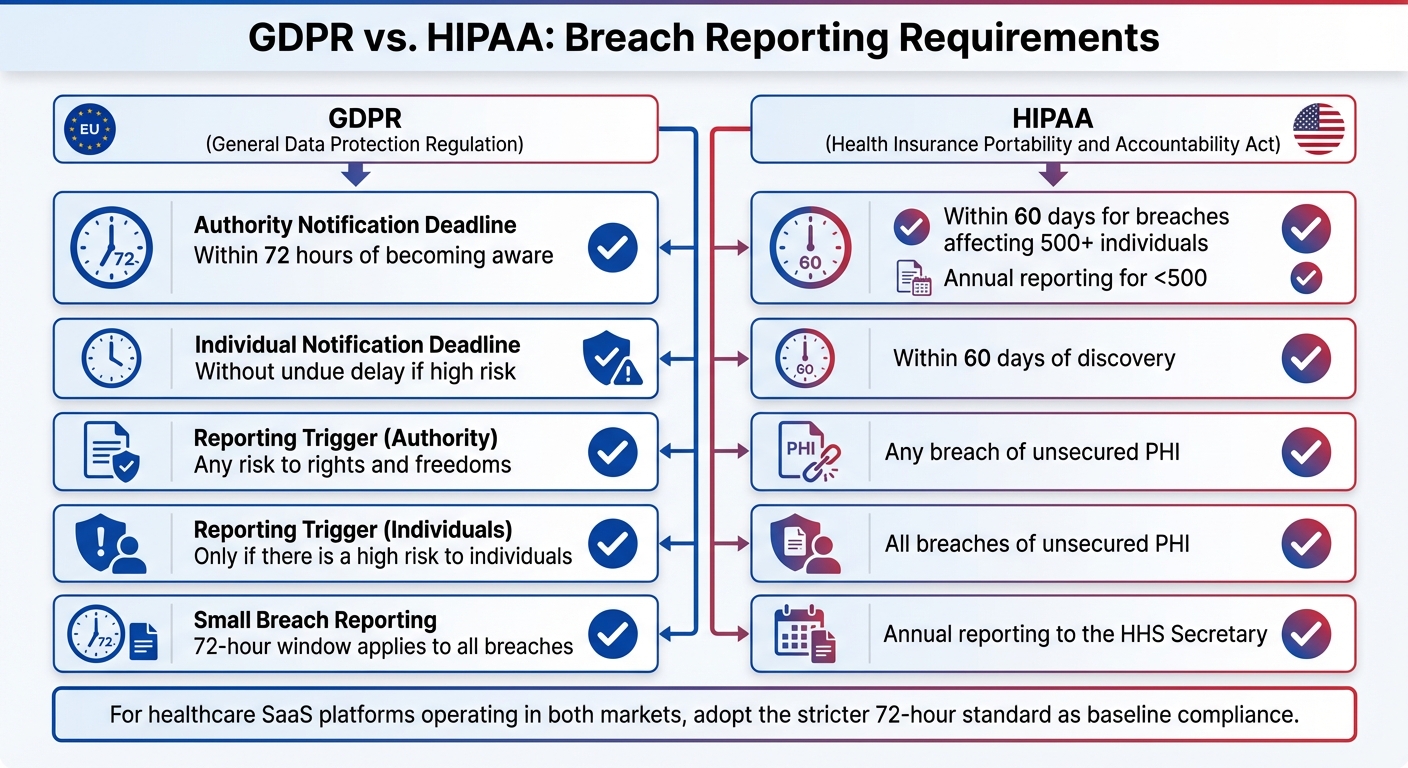
GDPR vs HIPAA Breach Reporting Requirements Comparison
When comparing GDPR's strict breach notification rules to HIPAA's requirements for U.S. healthcare providers, it's clear that businesses operating in both the EU and U.S. face distinct challenges. For healthcare SaaS providers catering to both markets, understanding the nuances of these frameworks is key to staying compliant and avoiding hefty penalties.
Under GDPR, breaches that pose a risk to individual rights must be reported within 72 hours. In contrast, HIPAA gives a longer timeline - 60 days for breaches involving 500 or more individuals. For smaller breaches (affecting fewer than 500 individuals), HIPAA requires annual reporting.
The criteria for notifying affected individuals also differ. GDPR mandates notification only when a breach presents a high risk to individuals' rights and freedoms. Meanwhile, HIPAA requires notification for any breach involving unsecured protected health information (PHI) within 60 days. As stated by HHS.gov:
An impermissible use or disclosure of protected health information is presumed to be a breach unless the covered entity or business associate... demonstrates that there is a low probability that the protected health information has been compromised.
Side-by-Side Comparison of GDPR and HIPAA Requirements
To make these differences easier to grasp, here’s a quick comparison:
| Feature | GDPR Requirements | HIPAA Requirements |
|---|---|---|
| Authority Notification Deadline | Within 72 hours of becoming aware | Within 60 days for breaches affecting 500+ individuals; annual reporting for <500 |
| Individual Notification Deadline | Without undue delay if high risk | Within 60 days of discovery |
| Reporting Trigger (Authority) | Any risk to rights and freedoms | Any breach of unsecured PHI |
| Reporting Trigger (Individuals) | Only if there is a high risk to individuals | All breaches of unsecured PHI |
| Small Breach Reporting | 72-hour window applies to all breaches | Annual reporting to the HHS Secretary |
This breakdown highlights the need for a consistent and proactive approach to breach reporting, especially for companies navigating both regulatory landscapes.
One way to streamline compliance is by adopting GDPR’s 72-hour reporting window as a baseline standard. Additionally, encryption can reduce GDPR reporting obligations if the data remains secure. However, HIPAA still requires notification for breaches involving unsecured PHI, so encryption alone may not eliminate all reporting duties.
Reducing Breach Risk Through Employee Training
Human error is behind 74% of all data breaches, making it the top threat to patient data security. Whether it’s sending an email to the wrong recipient, falling for a phishing scam, or using weak passwords, these seemingly minor mistakes can escalate into GDPR-reportable incidents. Addressing these risks through effective employee training is critical. A well-trained team becomes a powerful defense against breaches, helping to meet GDPR's strict reporting requirements.
Teaching Data Security Best Practices
Training shouldn’t be a once-a-year event. To be effective, it needs to be ongoing and tailored to the specific roles employees hold. A developer managing databases faces different challenges than a customer service representative handling patient inquiries. Generic training won’t cut it.
Start with role-specific training that addresses real-world scenarios. For example, teach employees to recognize phishing attempts through simulated exercises, adopt strong password habits with multi-factor authentication, and follow secure communication protocols. Quarterly refresher courses can help reinforce these practices. Additionally, tools like real-time nudges - automated alerts via Slack or email - can notify employees when they engage in risky behaviors, such as sharing files insecurely.
Training should also cover GDPR-specific requirements, such as identifying and routing Data Subject Access Requests (DSARs) within the one-month deadline. Employees must grasp that a breach isn’t limited to theft; it includes unauthorized access, accidental deletion, or even sending data to the wrong recipient.
Creating a Compliance-Focused Workplace
Technical safeguards are important, but a culture that prioritizes compliance is just as vital. Employees should feel safe reporting "near misses" or accidental incidents without fear of punishment. This openness allows organizations to address potential issues before they become full-blown breaches, aligning with GDPR’s proactive approach to incident response.
Make data protection training mandatory during onboarding so new hires understand security protocols before accessing patient data. As Kristy Gouldsmith, Data Protection, Privacy, and Cybersecurity Partner at Spencer West LLP, points out:
It's far cheaper and more efficient to embed your data protection bits at the beginning than create your shiny new thing and think, 'where are we going to put that data protection bit now?'
When employees realize that even small administrative errors can lead to fines of up to €10 million or 2% of global turnover, they’re more likely to integrate secure practices into their daily routines. Building this awareness from day one ensures a stronger, more prepared workforce.
Conclusion
The GDPR sets strict timelines for addressing data breaches. Healthcare SaaS platforms are required to notify the appropriate supervisory authority within 72 hours of becoming aware of a breach - unless it’s deemed unlikely to pose a risk to individuals.
Failing to act within this timeframe carries steep consequences. Non-compliance can lead to fines as high as €10 million or 2% of global annual revenue. However, the stakes go beyond financial penalties. Protecting patients from identity theft, fraud, and the exposure of sensitive medical details is a critical responsibility.
To ensure compliance, every breach should be meticulously documented. This includes recording the facts, assessing the impact, and detailing remedial steps taken. Such records not only demonstrate accountability but also help supervisory authorities confirm adherence to GDPR requirements.
Encryption can play a key role here. If breached data is rendered unreadable, reporting obligations may be reduced. Still, no single measure is enough. A strong incident response plan, regular system testing, and ongoing staff training are essential components of a comprehensive compliance strategy.
FAQs
What should a healthcare SaaS platform include in its incident response plan to meet GDPR requirements?
To meet GDPR requirements, a healthcare SaaS platform’s incident response plan needs to include precise steps for identifying, investigating, and managing personal data breaches. Key actions involve evaluating the risk to individuals, recording the incident, and informing the relevant supervisory authority within 72 hours of discovering the breach.
The notification must cover essential details, such as the nature of the breach, the type and amount of data involved, the potential effects on individuals, and the actions taken to reduce harm. Having a clear and structured process ensures timely and accurate reporting, which is critical to avoiding hefty fines and protecting the platform’s reputation.
How can healthcare organizations assess if a data breach puts patients at high risk?
Healthcare organizations can evaluate the risk of a data breach to patients by carefully examining several critical factors. These include the type and sensitivity of the compromised data, the chances it could be used to identify individuals, whether the information was accessed or misused, and any steps taken to reduce potential harm.
Adhering to established guidelines, such as those provided by HIPAA and the Office for Civil Rights (OCR), is essential in assessing the breach's impact. This approach not only helps determine if affected individuals need to be notified but also ensures compliance with data protection laws.
How can employee training help prevent patient data breaches?
Employee training plays a key role in safeguarding patient data from breaches. Organizations need to implement security awareness programs that equip staff with the skills to identify and handle potential threats, such as phishing attempts or suspicious emails. Training should also cover the correct methods for managing sensitive patient information, including secure access procedures and safe data-sharing practices.
It's equally important to establish clear guidelines for reporting potential breaches. Employees should understand how to respond promptly and escalate concerns when necessary. Regular training sessions, along with updates on new cybersecurity risks, ensure employees stay informed and compliant with regulations like HIPAA and GDPR. By prioritizing security education, healthcare organizations can better protect patient data and minimize the chances of breaches.
Author

Lidia Chesnokova, VP of Client Success at PatientPartner, drives patient engagement software strategy and personalized support solutions in healthcare.






