How to Build HIPAA-Compliant APIs for Data Integrity

Key Takeaways
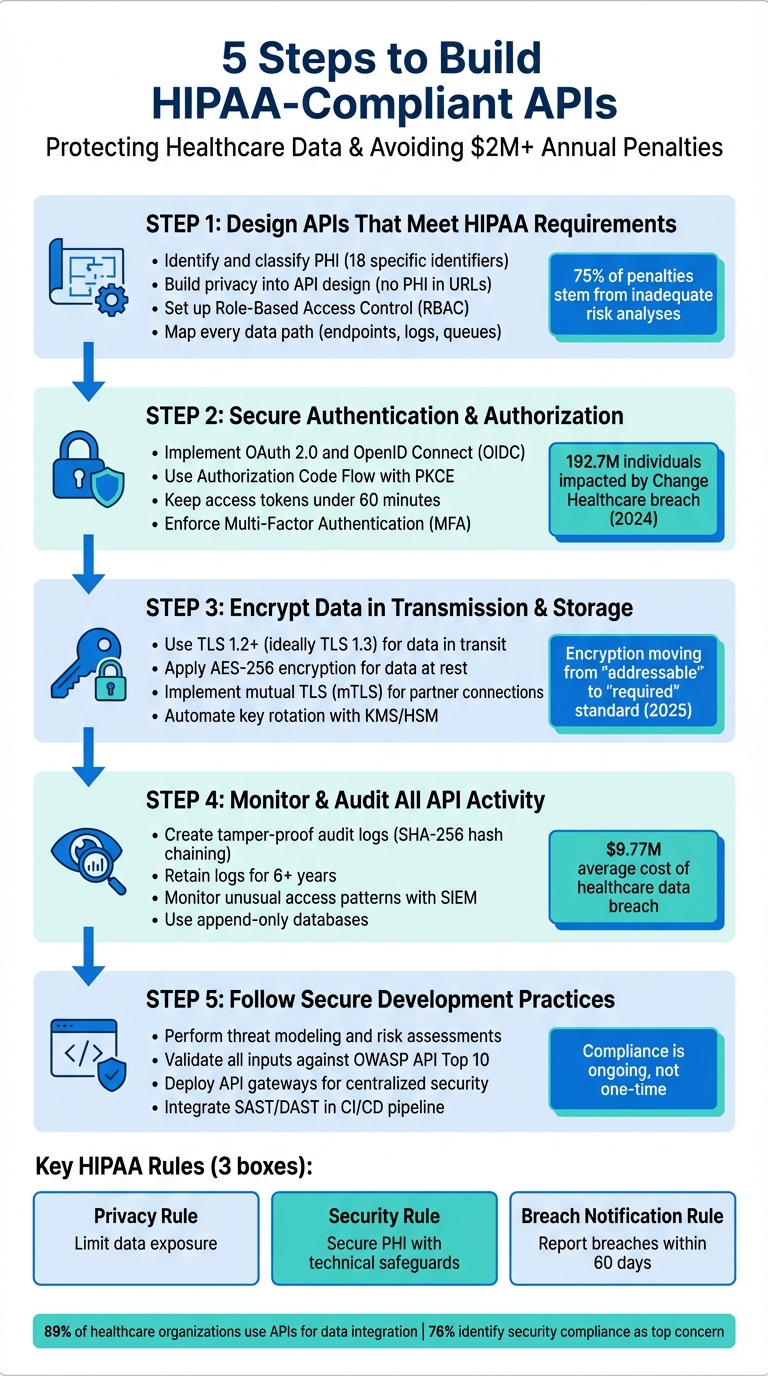
Building HIPAA-compliant APIs is essential for protecting sensitive healthcare data and avoiding significant fines, which can reach over $2 million per violation annually. APIs in healthcare must adhere to strict rules, including safeguarding Protected Health Information (PHI) through encryption, secure authentication, and detailed monitoring. Here’s a quick overview:
- Key HIPAA Rules: Privacy Rule (limit data exposure), Security Rule (secure PHI with technical safeguards), and Breach Notification Rule (report breaches within 60 days).
- PHI Protection: Identify and classify PHI, avoid exposing it unnecessarily, and ensure encryption during transmission and storage.
- Access Control: Use Role-Based Access Control (RBAC), OAuth 2.0, and Multi-Factor Authentication (MFA) for secure access.
- Monitoring and Logs: Maintain tamper-proof logs and monitor API activity to detect suspicious behavior.
- Secure Development: Conduct threat modeling, validate inputs, and use secure coding practices.
Following these steps ensures compliance, reduces risks, and protects patient data effectively.
5-Step Process for Building HIPAA-Compliant APIs in Healthcare
I Built a HIPAA-Compliant Medical Data Pipeline in Under 10 Minutes (John Snow Labs)
sbb-itb-8f61039
Step 1: Design APIs That Meet HIPAA Requirements
When building APIs, ensure HIPAA compliance is baked into the design process from the start. Waiting until post-deployment to address security can lead to costly mistakes. For example, in 2025, the Office for Civil Rights resolved 21 enforcement cases, and over 75% of the penalties stemmed from failures to conduct proper risk analyses. Keep detailed records of your security decisions during the design phase, as HIPAA requires these records to be retained for six years.
Identify and Classify Protected Health Information (PHI)
Protected Health Information (PHI) refers to any health-related data linked to one or more of 18 specific identifiers. While some identifiers are obvious, like names or Social Security numbers, others may be less apparent, such as IP addresses in server logs or email addresses tied to healthcare interactions.
"A user's email address combined with the fact that they have an account on your mental health app is PHI. Their IP address in your logs, tied to a healthcare visit, is PHI." - Waqar Habib, Full-stack Developer
To manage PHI effectively, map every data path in your API - this includes endpoints, background jobs, queues, and logs. Document where electronic PHI (ePHI) is created, received, or transmitted. This ensures you can adhere to the "minimum necessary" standard, where your API only processes or returns the PHI required for a specific task. For instance, a billing endpoint might only need a patient’s account number and insurance ID, not their full medical history or biometric data.
Don’t overlook metadata like device serial numbers, web URLs, or full-face images when classifying PHI. Conduct a documented risk analysis during the design phase to determine the safeguards needed for each data type. This mapping lays the groundwork for all subsequent security measures.
Build Privacy Into Your API Design
Once you’ve mapped PHI, implement privacy measures at every stage of your API design. For example, avoid including PHI in URL query parameters, as these can be stored in browser histories or server logs. Instead, pass sensitive data in request headers or POST bodies, ensuring it’s encrypted.
Sanitize error messages through middleware to prevent sensitive information - like patient emails or medical record numbers - from being exposed in stack traces sent to third-party tracking services.
Another key step is to configure automatic logoff mechanisms. Sessions should terminate or tokens should expire after 15 minutes of inactivity, a common standard for healthcare applications. Furthermore, design your API responses to return only the fields explicitly requested. For example, if a client requests a patient’s name and date of birth, the API should not inadvertently include additional details like their full address or phone number.
Set Up Role-Based Access Control (RBAC)
After embedding privacy measures, solidify access controls with Role-Based Access Control (RBAC). RBAC ensures users only have the permissions necessary for their role, following the principle of least privilege. Define clear roles - such as patient, physician, billing specialist, and administrator - and assign each role specific API permissions. For example, a patient should only access their own records and update their profile, while a billing specialist might view insurance details but not clinical notes.
To comply with HIPAA, assign unique identifiers to every user and client. When a request hits an endpoint like GET /v1/patients/{id}/record, verify on the server side that the authenticated user has a legitimate relationship with the patient. Never rely solely on client-side filtering to restrict access.
Use OAuth 2.0 and OpenID Connect for secure, time-limited, and scoped access tokens. These protocols align with HL7 FHIR standards for API authorization. For sensitive actions, implement Multi-Factor Authentication (MFA), as recommended by HIPAA.
Finally, log every access attempt in a centralized, tamper-proof audit log. Include details like user ID, resource accessed, action taken, and timestamp. Regularly review these logs to spot unusual activity, such as an account accessing an unusually high number of records. This proactive monitoring can help detect and mitigate potential breaches.
Step 2: Set Up Secure Authentication and Authorization
Once you’ve established privacy controls and designed your Role-Based Access Control (RBAC) structure, the next step is to implement strong authentication and authorization measures. These ensure that only verified users and systems can access your API. Below, we’ll break down how to authenticate users and enforce authorization effectively.
Implement OAuth 2.0 and OpenID Connect (OIDC)
Use OAuth 2.0 and OpenID Connect (OIDC) as your foundation for secure authentication and identity verification. These protocols are widely recognized for enabling seamless interoperability across healthcare systems. For applications that interact directly with patients, adopt the Authorization Code Flow with PKCE (Proof Key for Code Exchange). This approach prevents bad actors from intercepting authorization codes during the process:
"The Authorization Code flow is the most frequently used model and as it is regarded as the most secure model for securing public facing APIs for consumer applications." - Te Whatu Ora (Health New Zealand) API Standards
For backend integrations, rely on the Client Credentials Flow, secured with methods like mTLS (mutual TLS) or private key JWTs. Additionally, consider using SMART on FHIR, an extension of OAuth 2.0, which enforces fine-grained scopes such as patient/*.read. This aligns with HIPAA’s "minimum necessary" principle, ensuring access is limited to what’s absolutely required.
Manage Tokens Securely
Token security is critical. Keep access tokens short-lived - ideally under 60 minutes - and limit refresh tokens for single-page apps to a maximum of 24 hours. Shorter lifespans reduce the risk of misuse if a token is compromised. If your tokens include sensitive information, such as PHI (Protected Health Information) or PII (Personally Identifiable Information), encrypt them using JSON Web Encryption (JWE).
Automate private key rotation using a centralized Key Management Service (KMS) to maintain security and simplify operations. Additionally, provide a /revoke endpoint to allow users to invalidate tokens quickly in cases of device loss or suspected breaches.
The importance of robust token management was underscored by the February 2024 Change Healthcare ransomware attack, where attackers exploited a Citrix remote access portal without multi-factor authentication. This breach impacted nearly 192.7 million individuals and prompted the U.S. Department of Health and Human Services (HHS) to propose mandatory MFA under HIPAA starting January 2025.
Enforce Authorization on the Server Side
When it comes to authorization, always perform checks on the server side. Avoid relying on client-side checks, as they can be bypassed. The server must validate key elements of the JWT (JSON Web Token) on every request, including its signature, issuer (iss), audience (aud), and expiration (exp).
For example, if a request is made to GET /v1/patients/{id}/record, the server should confirm that the authenticated user has a legitimate relationship with the patient before granting access. This type of object-level authorization prevents unauthorized access to sensitive data.
Finally, centralize your authentication processes at the API Gateway. This allows you to handle authentication, enforce rate limiting, and validate schema before requests reach internal microservices. Centralizing these tasks strengthens your system while streamlining operations.
Step 3: Encrypt Data During Transmission and Storage
Once access is secure, the next step is to protect your data with strong encryption. Encryption acts as a shield, preventing unauthorized access to Protected Health Information (PHI), whether the data is being transferred between systems or stored in a database. According to a January 2025 Notice of Proposed Rulemaking by the HHS Office for Civil Rights, encrypting electronic PHI (ePHI) during transmission and storage will move from being an "addressable" specification to a "required" standard under HIPAA.
Use TLS to Encrypt Data in Transit
To secure data in transit, enforce TLS 1.2 or higher (ideally TLS 1.3). Terminate TLS at an API gateway or Web Application Firewall (WAF) configured with robust security settings to ensure consistent protocol versions. Disable outdated protocols like TLS 1.0 and 1.1, along with weak cipher suites, to guard against downgrade attacks. For added security, implement mutual TLS (mTLS) for trusted partner connections and internal service-to-service traffic. This ensures both the client and server authenticate each other.
Additionally, deploy HTTP Strict Transport Security (HSTS) to ensure browsers and clients communicate with your API exclusively over secure HTTPS connections. When combined with encryption for data at rest, these measures provide comprehensive protection.
Apply AES Encryption to Data at Rest
For data stored in databases or other systems, use AES-256 encryption in authenticated modes like AES-GCM to maintain both confidentiality and integrity. A best practice is to implement envelope encryption, where each dataset is secured with a unique Data Encryption Key (DEK) that is then protected by a Key Encryption Key (KEK). Store KEKs in a Hardware Security Module (HSM) or a FIPS-validated Key Management Service (KMS).
Depending on your needs, you can apply encryption at different levels, such as full disk, virtual disk, or file-level encryption. Properly encrypted PHI that is rendered "unusable, unreadable, or indecipherable" qualifies for the safe harbor provision. This could exempt your organization from mandatory breach notifications if such data is lost or stolen.
Manage and Rotate Encryption Keys
Effective encryption depends on solid key management practices. Store decryption keys separately in a dedicated key management service like Azure Key Vault, AWS Secrets Manager, or HashiCorp Vault. Automate key rotation to limit exposure in the event of a compromise, and use Role-Based Access Control (RBAC) to restrict who can access these keys.
Set up rotation schedules to ensure new data is encrypted with the latest key, while older data can be re-encrypted during maintenance windows. Use key versioning to track changes and maintain control. Ensure all cryptographic modules comply with FIPS 140-3 standards for auditable security.
Step 4: Monitor and Audit All API Activity
After designing secure APIs, the next step to ensure HIPAA compliance is implementing thorough monitoring and auditing processes. These measures are essential for tracking all API activity and detecting potential breaches early. HIPAA regulations require organizations to log and review all interactions involving electronic Protected Health Information (ePHI). Specifically, the HIPAA Security Rule (45 CFR § 164.312(b)) mandates that you "record and examine activity in information systems that contain or use electronic protected health information". Without detailed audit logs, it's nearly impossible to demonstrate compliance during HHS audits or quickly identify security incidents.
Create Tamper-Proof Audit Logs
Simply maintaining logs isn't enough - they must be secure and tamper-resistant. Piyoosh Rai from Towards AI emphasizes this point: "HIPAA doesn't just want logs. It wants logs you can trust. Logs that can prove they haven't been altered. Logs that can survive a hostile insider with database access". A real-world example highlights the risks: a contractor accessed 47,000 patient records over 94 days without detection because they deleted mutable audit logs. This oversight led to a $2.3 million fine and $340,000 in investigation costs.
To build reliable audit logs, include key details like user identity, actions performed, timestamps, origin, context, and results. Use cryptographic hash chaining (e.g., SHA-256) to link each log entry to the previous one. This ensures that any tampering breaks the chain, making alterations immediately detectable. For high-volume APIs, consider using Merkle trees, which allow for efficient integrity checks without scanning the entire log chain.
Additionally, configure your audit database as append-only to prevent unauthorized modifications. Use a dual-storage approach: an append-only primary database for active queries and an immutable archive, such as AWS S3 Object Lock or Azure Immutable Blob Storage, for long-term retention. HIPAA requires you to retain these logs for at least six years from their creation or last use.
Once your logs are tamper-proof, the next step is to actively monitor them for suspicious activity.
Identify Unusual API Usage Patterns
Secured logs are only valuable if they’re actively monitored. Set up automated tools to continuously verify the integrity of your logs by checking hash chains and sequence numbers. Missing entries or gaps could be a red flag for tampering. Pay close attention to "Access Denied" events and role-based access control (RBAC) failures as these can indicate early signs of a breach.
To protect your logging system, implement rate limiting to defend against "log flooding" attacks that could overwhelm your system or deplete storage. Use a dedicated logging service with exclusive write access to the audit database. Integrate this system with a Security Information and Event Management (SIEM) platform to enable real-time monitoring and alerts for unusual access patterns. Additionally, enforce automatic session timeouts (e.g., after 15 minutes of inactivity) to ensure logs accurately reflect active user sessions.
Use Logs to Prove Compliance
Audit logs do more than just detect breaches - they also serve as critical evidence during HIPAA audits. Regulators often rely on these records to verify compliance. However, many healthcare AI teams fail to create logs that meet regulatory standards, particularly in proving their integrity. To avoid this pitfall, ensure your logs are indexed, searchable, and stored separately from application logs to reduce the risk of a single point of failure.
The stakes are high: the average cost of a healthcare data breach is $9.77 million. To safeguard your organization, automate integrity checks that compare primary storage with immutable archives to identify tampering. Finally, remember that even access to the audit logs must be monitored and restricted. HIPAA requires that log access is tracked to prevent unauthorized viewing or manipulation. By taking these steps, your logs will not only detect breaches but also provide the solid proof needed to demonstrate compliance.
Step 5: Follow Secure Development Practices
Secure development practices form a critical part of achieving HIPAA compliance. These practices ensure that security is embedded at every stage of API development. With over 75% of penalties in 2025 stemming from inadequate risk analyses, the importance of secure development cannot be overstated.
Perform Threat Modeling and Risk Assessments
Before writing a single line of code, take a step back and map out every possible pathway for ePHI. This includes background jobs, retries, dead-letter queues, and third-party integrations. One common pitfall is overlooking "Shadow APIs" - those legacy endpoints that often escape security monitoring. These can serve as unnoticed vulnerabilities, providing attackers with an entry point.
Threat modeling allows you to identify risks like Broken Object Level Authorization (BOLA) and Server-Side Request Forgery (SSRF) before they become problems. It also helps you enforce the "minimum necessary" principle by determining which API fields should be masked, tokenized, or eliminated entirely. To catch vulnerabilities early, integrate tools like SAST and DAST into your CI/CD pipeline.
The ransomware attack on Change Healthcare in 2024 highlighted the need for more robust security measures, leading to a push for mandatory MFA in 2025. Once risks are identified, the next step is translating those insights into secure coding practices.
Write Secure Code
Writing secure code starts with strict input validation. Every payload should be validated against predefined schemas and contracts to prevent injection attacks and other vulnerabilities listed in the OWASP API Security Top 10. Use field-level filtering tools, such as JSONata, to strip out unnecessary PHI.
Error handling is another area that requires attention. Avoid including PHI in error messages or stack traces sent to external services. Instead, log only essential metadata, such as request IDs and actor identities. Encryption, while important, is just one piece of the puzzle - security needs to be layered throughout.
When integrating third-party tools, ensure they are willing to sign a Business Associate Agreement (BAA). If they won’t, halt the technical evaluation immediately. Transmitting PHI through a service without a BAA is a direct HIPAA violation. Additionally, use centralized Key Management Services (KMS) or Hardware Security Modules (HSM) to automate key rotation and eliminate hard-coded credentials.
Once your code is secure, an API gateway can provide centralized control over access and security.
Deploy API Gateways for Centralized Security
An API gateway acts as a central point for enforcing security policies. It blocks insecure requests while managing authentication (using OAuth 2.0, JWT, or mTLS) and authorization (RBAC) consistently across all endpoints. Gateways also validate schemas to ensure incoming data matches expected formats, rejecting unknown fields to avoid excessive data exposure.
To prevent API abuse and DDoS attacks, employ rate limiting and throttling at the gateway level. For example, in 2025, a multinational bank cut unauthorized login attempts by 87% in six months by deploying an API gateway with OAuth 2.0, MFA, rate limiting, and behavioral analytics to stop credential stuffing attacks. Similarly, a telehealth provider achieved full HIPAA compliance and eliminated unsecured API calls by implementing a gateway with TLS 1.3 encryption and real-time monitoring.
Integrating your gateway with a Web Application Firewall (WAF) adds another layer of protection by filtering out malicious payloads like SQL injection and cross-site scripting (XSS). Gateway logs can be exported to a SIEM platform for real-time monitoring and immutable audit trails. As AppSentinels puts it:
"The API gateway is not just a pass-through layer - it is the nerve center for managing API security, efficiency, and governance".
For legacy healthcare systems that lack native HIPAA compliance features, an API gateway can bridge the gap by adding modern security controls like encryption and MFA. This ensures older infrastructure meets today’s rigorous compliance standards.
Conclusion: Building Compliant APIs for Healthcare
Creating HIPAA-compliant APIs requires a multi-layered security approach, continuous monitoring, and strict adherence to regulations. In 2024, healthcare breaches cost organizations an average of $9.77 million, with penalties reaching as high as $2,190,294 per violation. Compliance isn’t just a legal obligation - it’s essential for protecting both patients and your business.
To build a secure API, you need to focus on layered defenses and ongoing oversight. The five key steps - designing with privacy in mind, implementing secure authentication, encrypting data, maintaining audit logs, and following secure development practices - are the backbone of compliance. As Jim Kutz points out, "Compliance is not a one-time project". Regular risk assessments, annual penetration testing, and rotating credentials every quarter are critical to staying ahead of evolving threats and regulatory updates.
The regulatory environment is becoming stricter. For instance, the 2025 Notice of Proposed Rulemaking (NPRM) will make encryption and multi-factor authentication (MFA) mandatory for all systems handling electronic protected health information (ePHI). These safeguards can no longer be treated as optional - they must be incorporated into API design from the start. By embedding these principles at every stage of development, you’ll not only meet new regulatory demands but also strengthen your API’s security.
Healthcare increasingly relies on real-time data exchange. Techniques like zero-retention architectures, pass-through proxies, and adhering to the "minimum necessary" principle allow your API to balance innovation with strong security. With 89% of healthcare organizations now using APIs for data integration, and 76% identifying security compliance as their top concern, the message is clear: security must be treated as an ongoing operational priority, not a one-time task. By combining careful planning, secure coding practices, and centralized controls through API gateways, you can build APIs that safeguard patient data, meet compliance standards, and enable the future of connected care. At PatientPartner, we’re committed to applying these best practices to enhance connected care and improve patient outcomes.
FAQs
What counts as PHI in API requests, logs, and metadata?
Protected Health Information (PHI) in API requests, logs, and metadata refers to any details that could reveal a patient's identity. This includes personal identifiers, medical records, or treatment specifics. Proper safeguards are essential to ensure compliance with HIPAA regulations.
How do I implement object-level authorization so users can only access the right patient records?
To make sure users only access the appropriate patient records, implement role-based access controls (RBAC) in your API. Start by using secure authentication protocols like OAuth 2.0 to confirm user identities. Once authenticated, assign permissions based on the user’s role - for example, a healthcare provider or authorized staff member.
Incorporate access control checks directly into your API endpoints to enforce these permissions. This approach helps restrict access to sensitive data, ensuring compliance with HIPAA regulations while safeguarding patient privacy and data integrity.
How can I make audit logs tamper-proof and HIPAA-ready for a 6-year retention period?
To keep audit logs tamper-proof and meet HIPAA's 6-year retention requirement, you'll need a secure setup with strong cryptographic protections. This means using encrypted storage, integrity checks, and tools like hashing and digital signatures to verify the logs' authenticity. Store these logs in environments with strict access controls, and make it a habit to perform regular validation to spot any issues.
Additionally, implement a clear retention policy that aligns with HIPAA's rules. This ensures logs are securely preserved for the full required period, all while guarding against unauthorized changes.